Meet Intercept
A unified application security platform with nine integrated scan modules, AI-powered threat modeling, and a single score that tells you exactly where you stand. Intercept gives engineering teams meaningful visibility into their environment and security teams the findings they need — all from one platform.
Free during Early Access. Invites sent in batches as we onboard each cohort.
One Number. Complete Clarity.
The Intercept Score aggregates findings across all nine modules into a 0–1000 rating with letter grades per category. No more spreadsheet triage.
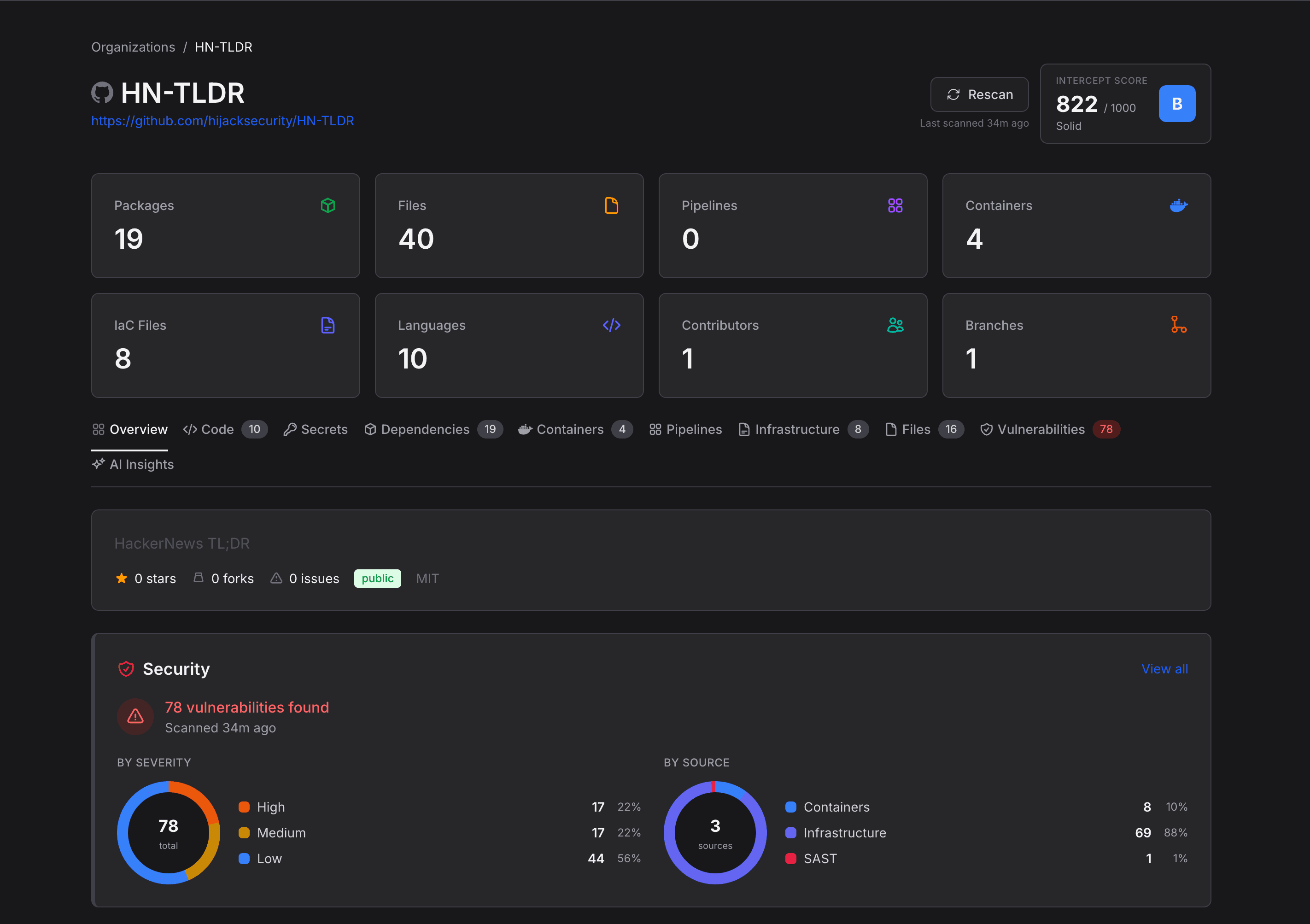
Nine Modules. One Score.
Every scan module feeds into the Intercept Score — a single 0–1000 rating that tells your team exactly where security stands across every domain.
Nine Integrated Scan Modules
Start with battle-tested open-source scanners out of the box — then plug in your own enterprise tools when you're ready
Repository Governance
GovernanceMaps repository health, development practices, and security hygiene — language breakdowns, contributor activity, branch protection, commit signing, CODEOWNERS, permissions, and security feature adoption. Useful for both engineering leads and security teams.
SBOM Generation
ComplianceProduces CycloneDX 1.6 compliant Software Bill of Materials with dual-source dependency extraction across 11 ecosystems — including auto-normalization of encoded manifests that other tools silently miss.
Vulnerability Intelligence
PackagesCross-references dependencies against 4 vulnerability databases with EPSS exploit prediction scoring, CVSS vectors, CWE classifications, and fix version tracking — prioritizing by real-world exploitability, not just severity.
Secret Detection
Secrets180+ detection rules with entropy analysis and a zero-knowledge architecture — redacted secrets never enter the pipeline. Private keys are elevated to CRITICAL severity because they enable direct system compromise.
Static Analysis (SAST)
CodeCode vulnerability detection across 30+ languages with intelligent severity elevation — findings in categories like injection, XSS, or deserialization are automatically promoted based on OWASP category and CWE classification.
Container Security
ContainersDeep Dockerfile analysis beyond simple linting — base image tracking, multi-stage build configuration, system package inventory with version pins, user context, health checks, and exposed port auditing.
Infrastructure as Code
IaCScans 5 IaC frameworks — Terraform, Kubernetes, Helm, CloudFormation, and Docker Compose — extracting resource inventories and provider configurations, then checking for insecure defaults, missing encryption, and overly permissive access.
Pipeline Security
PipelinesAudits CI/CD configurations across 9 platforms with supply chain inventory — every third-party action, orb, and task is cataloged, SHA-pinning status checked, and untrusted dependencies flagged.
AI-Powered Analysis
AIFive structured analyses per repo: business purpose classification, architecture mapping, tech stack detection, STRIDE threat modeling, and security maturity assessment. Engineering teams get architecture docs and stack inventory. Security teams get threat models and maturity ratings.
Works With Your Stack
Intercept integrates with the tools and platforms you already use
Package Ecosystems
8+CI/CD Platforms
9IaC Frameworks
5Know Every Package in Your Environment
Intercept inventories every dependency across all your repositories — broken down by ecosystem, version, and vulnerability count. See exactly what's in your supply chain before attackers do.
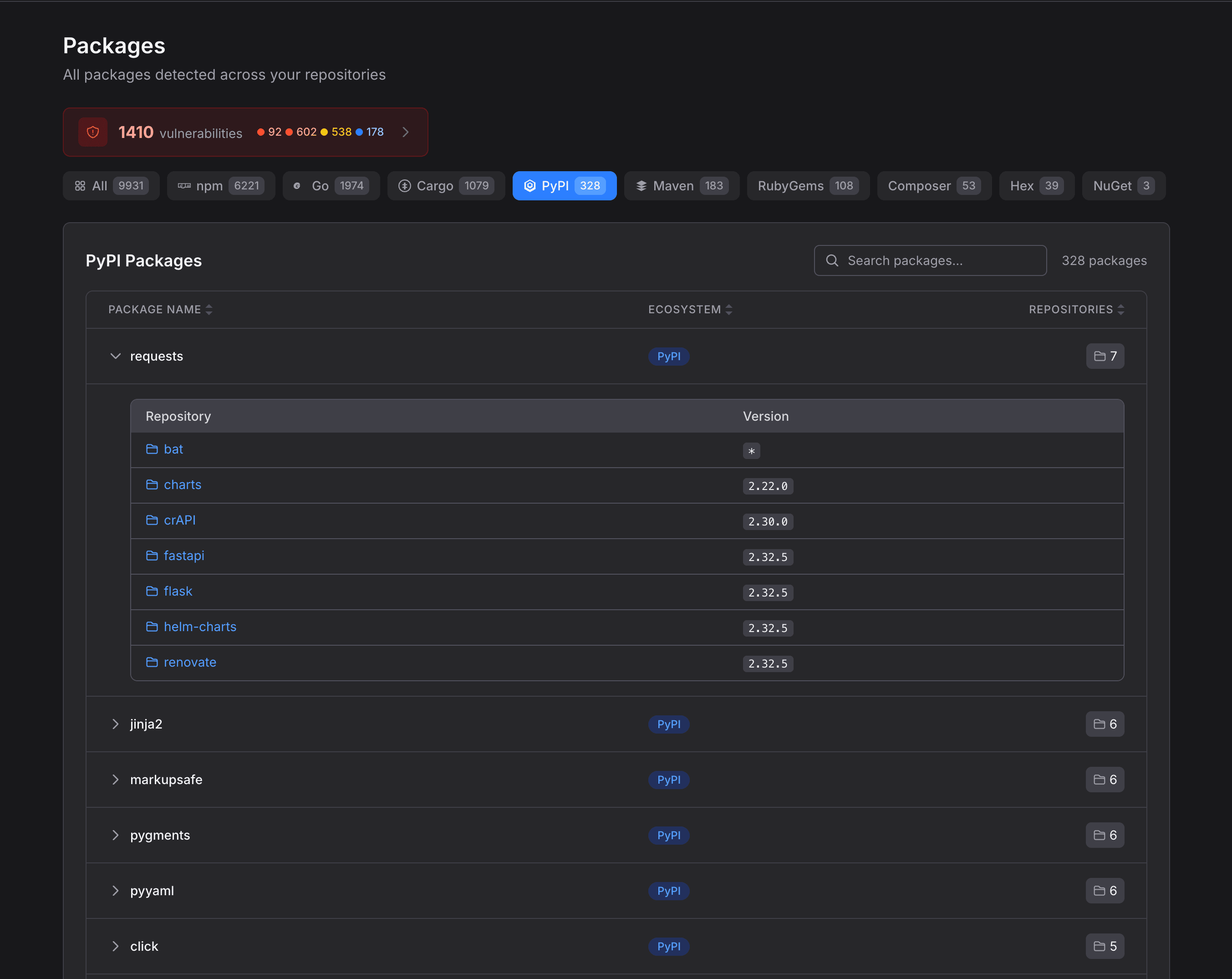
Multi-Ecosystem Inventory
Automatic detection across npm, Go, PyPI, RubyGems, Maven, Hackage, and more. One unified view of every package your organization depends on.
Cross-Repo Package Tracking
See which repositories use each package and at what version. Drill down to understand blast radius when a dependency is compromised.
Vulnerability Severity Breakdown
Vulnerabilities categorized by severity — critical, high, medium, and low — so you can prioritize remediation based on actual risk to your environment.
Continuous Monitoring. Instant Response.
Intercept continuously monitors OSV, GitHub Advisory, CISA KEV, and NVD feeds — cross-referencing your environment so you know the moment a new vulnerability affects your stack.
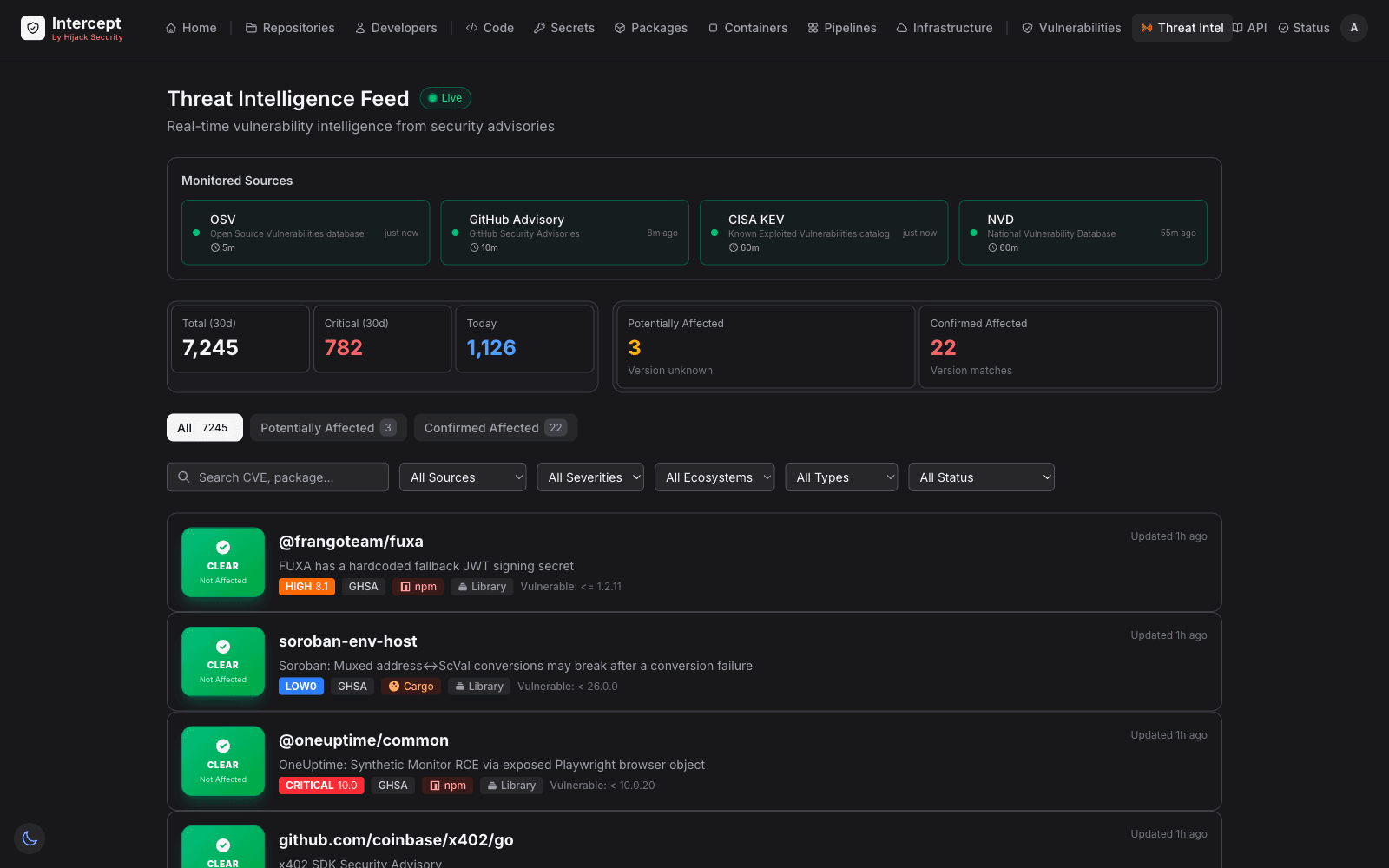
Automatic Exposure Analysis
When a new CVE is published, Intercept automatically searches your dependencies across all tenants and repos. Version-aware matching with HIGH/MEDIUM/LOW confidence levels.
Configurable Alerting
Alert rules with severity thresholds, repository scoping, ecosystem filters, and package pattern matching. Email and in-app notifications with 24-hour deduplication.
Resolution Tracking
Track every finding with resolution statuses: fixed, accepted risk, false positive, mitigated. Full audit trail with history, notes, and verification links.
Built for the AI Era
Capabilities that don't exist in legacy security scanners
Threat Intelligence
Real-time vulnerability feeds from OSV, CISA KEV, GitHub Advisory, and NVD with EPSS exploitability scoring. Know which vulnerabilities are actually being exploited in the wild.
Developer Posture Agent
Lightweight agent inventories developer environments — IDEs, extensions, AI tools, MCP servers, security practices. Understand the human side of your attack surface.
MCP Risk Detection
Map which MCP servers your developers use, what permissions they have, and where the risks are. The first security platform to address AI tool infrastructure risk.
AI Tool Inventory
Track every AI tool, copilot, and coding assistant across your organization. Understand adoption patterns and identify shadow AI usage with security implications.
Skip the Tool Sprawl. Request Access.
Intercept is in Early Access. Nine scan modules, one score, no tool sprawl — request an invite and we'll get you in.
Free during Early Access. Invites sent in batches as we onboard each cohort.