Complete Application Security.
Beyond Source Code.
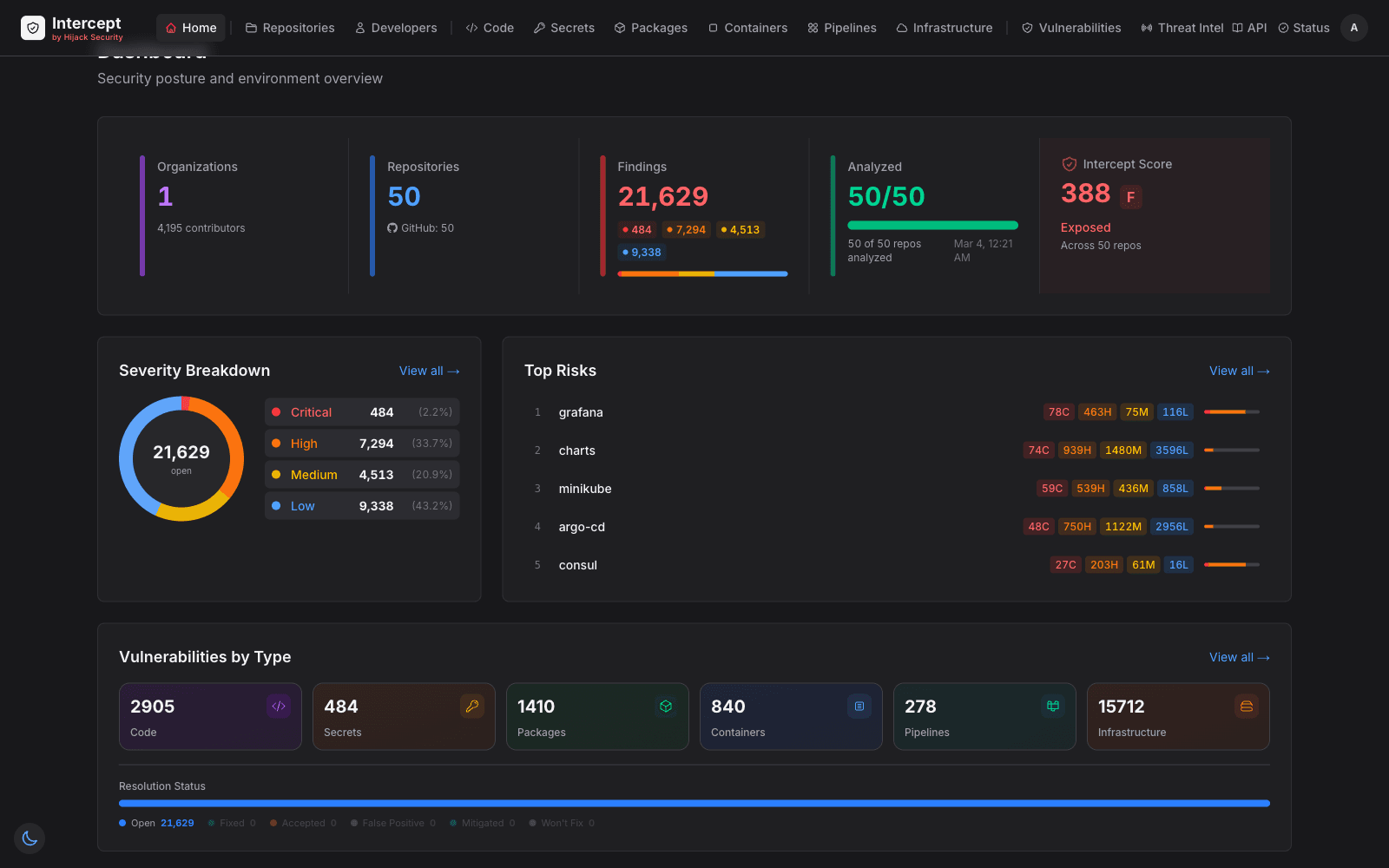
Intercept scans your platforms, repos, code, packages, secrets, containers, pipelines, infrastructure as code, and developer environments — one platform covering your entire application surface.
When a new vulnerability drops, you know immediately if you're affected, exactly where, and what to fix. No scrambling across dashboards. No blind spots.
Free at launch. No credit card required.
Get Started in Seconds
Sign in with GitHub, install the app, and import your repos. That's it — Intercept starts scanning immediately.
Four Pillars. Complete Visibility.
Intercept stretches across your entire software supply chain — from the platforms you build on, to the repos you manage, to the code you ship, to the developers who write it.
Security Across the Entire Lifecycle
Intercept doesn't just scan your code — it provides security at every phase of the software development lifecycle. From planning and threat modeling through coding, building, testing, releasing, deploying, and continuous monitoring.
Platforms
Audit the platforms you build on — settings, configurations, installed apps, and third-party integrations.
Repositories
Assess repository health, governance, and security best practices across your org.
Code
Scan everything in your codebase — source code, dependencies, secrets, infrastructure definitions, pipelines, and containers.
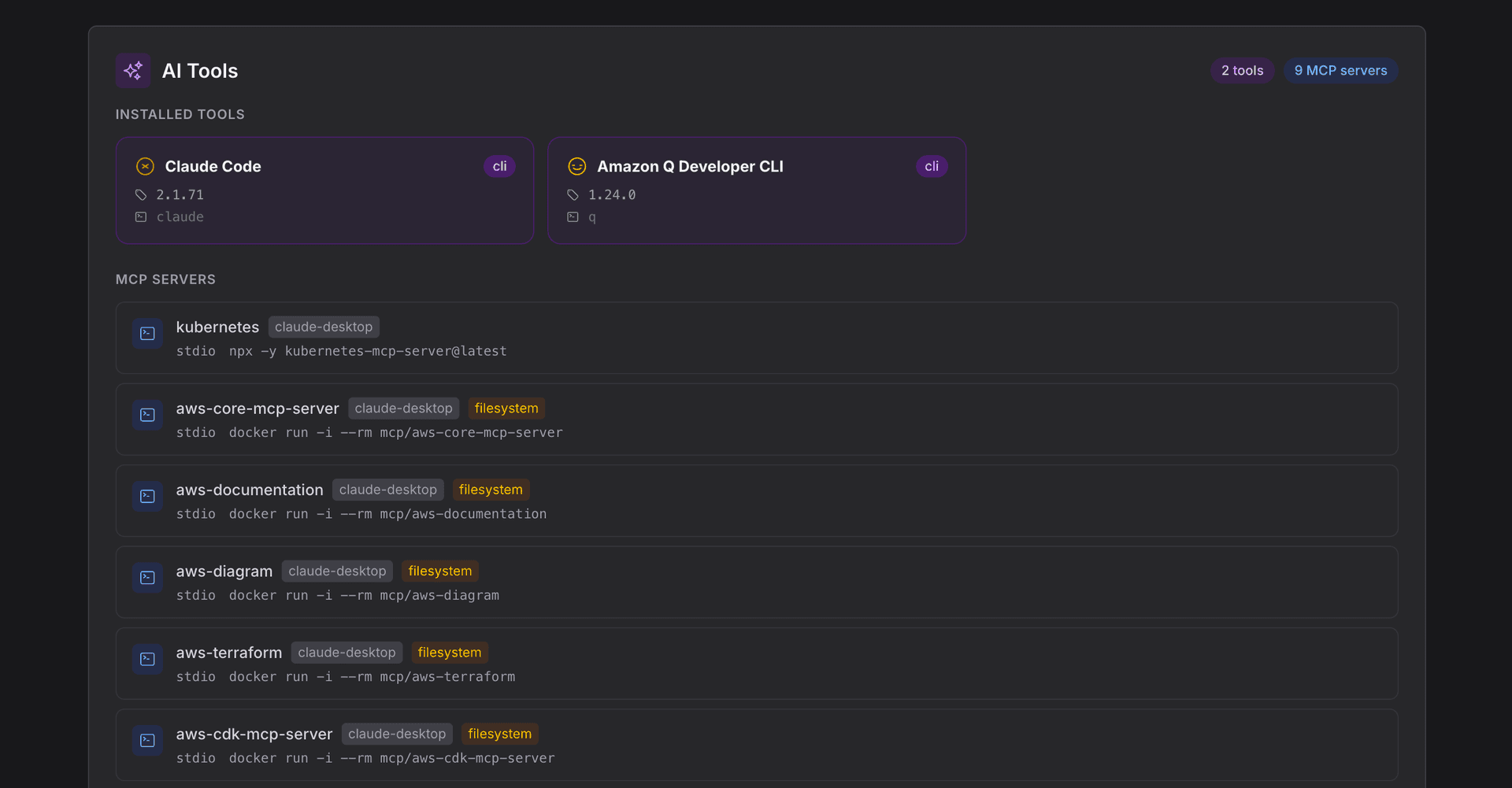
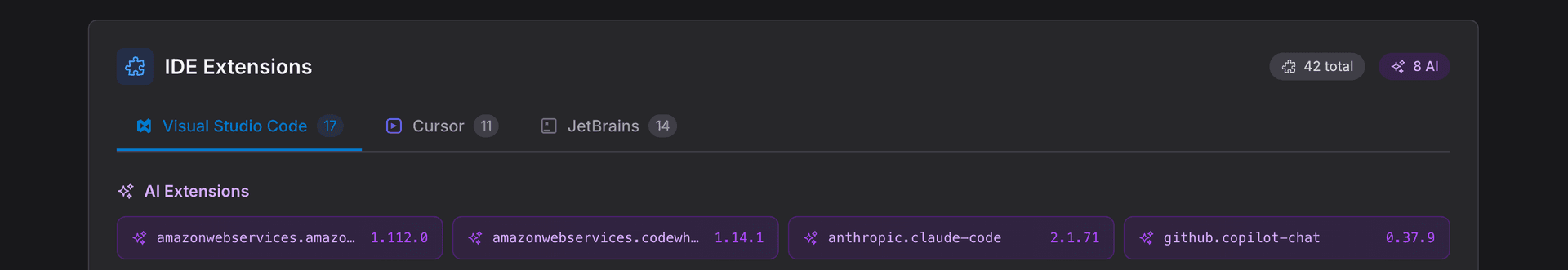
Developers
Map the human side of your attack surface — developer machines, tools, AI assistants, and MCP server configurations.
Continuously Scanned. Continuously Monitored.
Every repo scanned periodically and on every push. Full nine-module pipeline runs automatically so your security posture is always current.
Four feeds (OSV, NVD, GHSA, CISA KEV) monitored in real time. New critical and high severity CVEs trigger immediate exposure analysis across your environment.
Configurable alert rules with severity thresholds, repository scoping, and ecosystem filters. Email and in-app notifications with deduplication.
Intercept exposes findings via API — enabling AI coding agents to assist with remediation directly in your workflow. MCP server support coming soon.
Platforms
Audit the platforms you build on — settings, configurations, installed apps, and third-party integrations.
Repositories
Assess repository health, governance, and security best practices across your org.
Code
Scan everything in your codebase — source code, dependencies, secrets, infrastructure definitions, pipelines, and containers.
Developers
Map the human side of your attack surface — developer machines, tools, AI assistants, and MCP server configurations.
Every repo scanned periodically and on every push. Full nine-module pipeline runs automatically so your security posture is always current.
Four feeds (OSV, NVD, GHSA, CISA KEV) monitored in real time. New critical and high severity CVEs trigger immediate exposure analysis across your environment.
Configurable alert rules with severity thresholds, repository scoping, and ecosystem filters. Email and in-app notifications with deduplication.
Intercept exposes findings via API — enabling AI coding agents to assist with remediation directly in your workflow. MCP server support coming soon.
Partial Coverage Is No Coverage
Most teams run 5-10 disconnected scanners. Each one covers a slice. But when a new CVE drops at 2am, you can't answer the only question that matters: are we affected?
- ✗Gaps between tools mean vulnerabilities slip through unnoticed
- ✗No single inventory of what you have — code, packages, containers, pipelines, secrets, IaC
- ✗When a threat hits, you're scrambling across dashboards instead of responding
- ✓Intercept gives you complete visibility so you can detect, identify, and respond — instantly
Complete Security. Instant Response.
Most scanners check one thing and serve one team. Intercept covers everything — giving engineering teams real visibility into their environment and security teams the findings they need to act.
Visibility for Every Team
CoreIntercept produces two kinds of data: general engineering insights — language breakdowns, dependency inventories, architecture maps, tech stack detection, development velocity — and deep security analysis. Where we can't scan directly, like deployment targets or full image layers, we provide guidance so you're still covered. Engineering and security teams both work from the same source of truth.
AI-Era Security
Industry FirstInventory AI coding agents (GitHub Copilot, Cursor, Claude Code, Aider) and MCP servers across your team. Detect credential access, shell execution, and network exposure risks in MCP server configurations — an attack surface no other tool covers.
AI-Powered Analysis
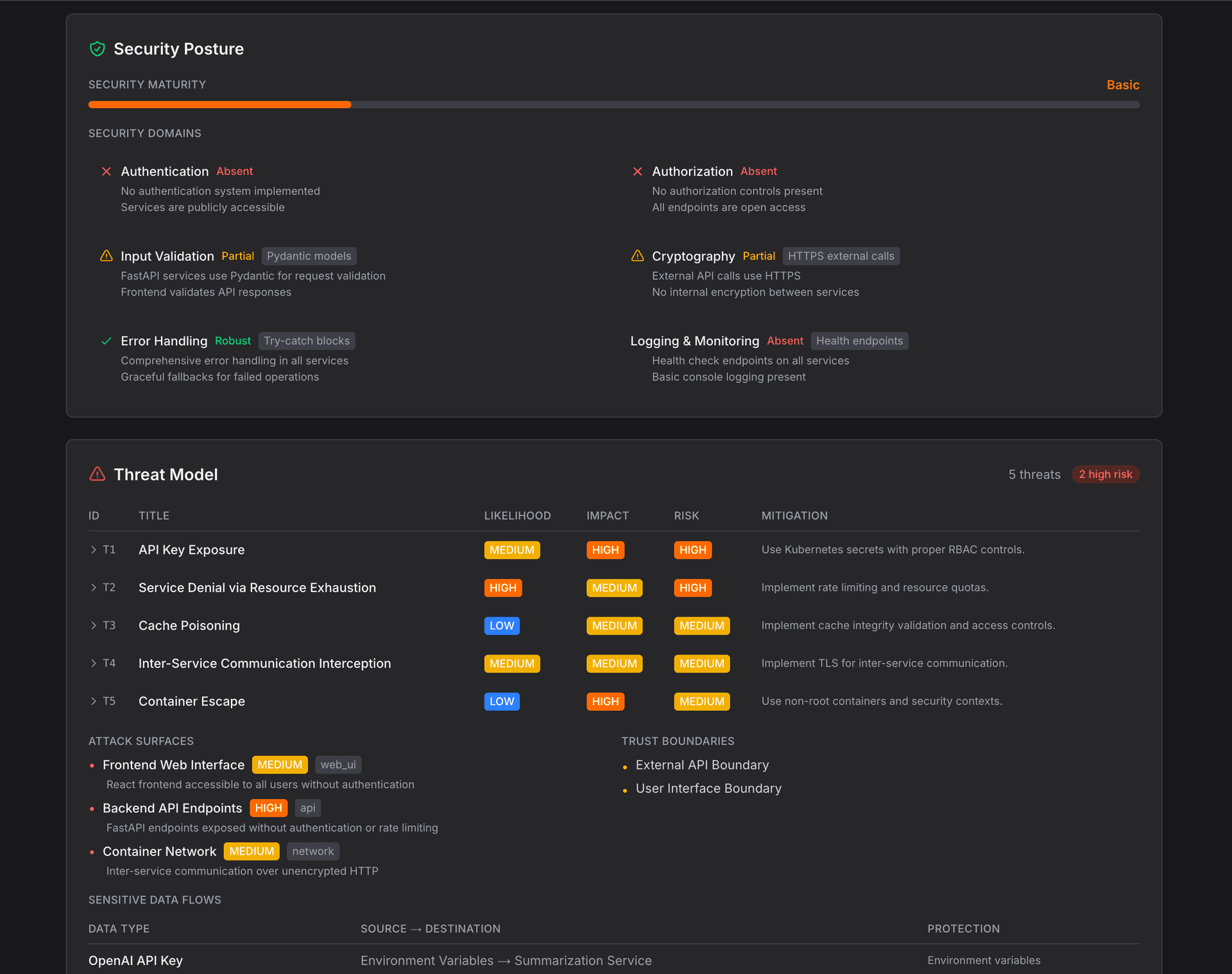
AI-PoweredAutomated STRIDE threat modeling, security architecture mapping, business purpose classification, and security maturity review — all from a single AI-powered analysis per repo. Plus, findings exposed via API and MCP for AI-assisted remediation.
One Score, Full Picture
ArchitectureThe Intercept Score aggregates findings across 7 weighted categories into a single 0–1000 rating with letter grades. One number that tells your team exactly where security stands — from individual repos to the entire org.
AI-Native Security Intelligence
The first security platform that inventories AI tools, audits MCP server configurations, and generates STRIDE threat models — automatically.
AI Tool Inventory & MCP Risk Detection
Map which AI coding tools your developers run, which MCP servers they've configured, and what permissions those servers have — filesystem access, environment variables, API credentials, and shell execution capabilities. Risks you can't fix if you can't see them.
AI-Powered Security Analysis
Automated STRIDE threat modeling, security posture assessment, and maturity scoring — all from a single AI analysis per repo. Attack surfaces, trust boundaries, and sensitive data flows mapped automatically.
See it for yourself — join the waitlist.
Nine Modules. One Score.
Every scan module feeds into the Intercept Score — a single 0–1000 rating that tells your team exactly where security stands across every domain.
Security That Fits How You Build
Whether you're a solo developer shipping with AI or an enterprise securing hundreds of repos — Intercept scales to your workflow.
Ready to See Everything?
Join the waitlist. Be first to experience Intercept — nine scan modules, one score, zero tool sprawl.
Free at launch. No credit card required.